| 失效链接处理 |
|
Cryptography - Theory And Practice,Douglas Stinson,1995 PDF 下载
本站整理下载:
相关截图:
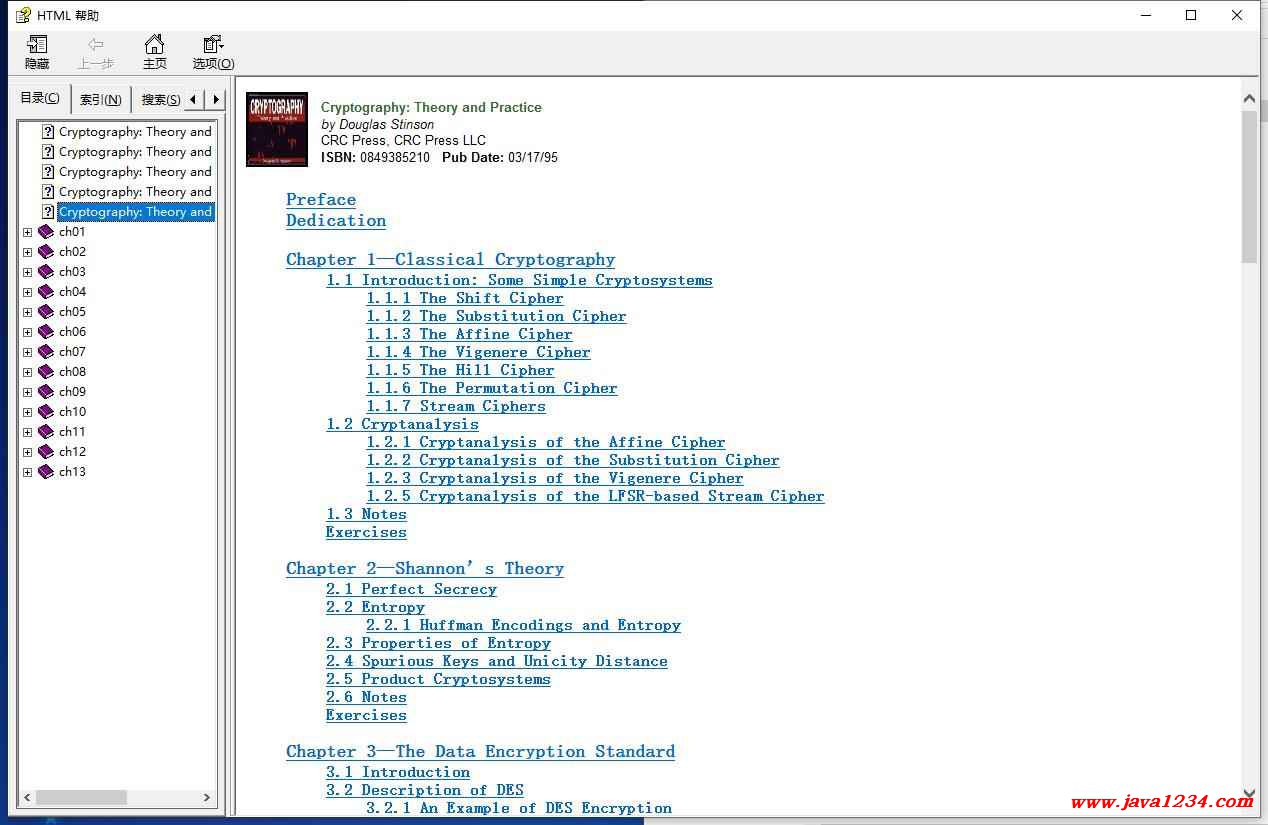
主要内容:
Index
abelian group, 4, 116, 184
accept, 385
access structure, 331
threshold, 332, 333
active adversary, 258
additive identity, 3
additive inverse, 3
adjoint matrix, 16
adversary
active, 258
passive, 258
Affine Cipher, 8, 8-12
cryptanalysis of, 26-27
affine function, 8
Affine-Hill Cipher, 41
algorithm
deterministic, 129
Las Vegas, 139, 171, 234
Monte Carlo, 129, 129
probabilistic, 129
associative property, 3
of cryptosystems, 66
authentication code, 304, 304-323
combinatorial bounds, 311-313
deception probability, 305, 306-313, 319-323
entropy bounds, 321-323
impersonation attack, 305, 306-308
orthogonal array characterization, 319-320
substitution attack, 305, 307-309
authentication matrix, 306
authentication rule, 305
authentication tag, 305
authorized subset, 331
minimal, 332
Autokey Cipher, 23, 23
basis, 332
Bayes’ Theorem, 45, 60, 135, 340, 341
binding, 399
binomial coefficient, 31
birthday paradox, 236
bit commitment scheme, 399, 398-401, 405-407
blob, 399
block cipher, 20
Blom Key Predistribution Scheme, 261, 260-263
Blum-Blum-Shub Generator, 371, 370-377, 379
Blum-Goldwasser Cryptosystem, 380, 379-382
boolean circuit, 333
fan-in, 333
fan-out, 333
monotone, 333
boolean formula, 333
conjunctive normal form, 337
disjunctive normal form, 334
Bos-Chaum Signature Scheme, 216, 215-217
Brickell Secret Sharing Scheme, 344, 343-348
Caesar Cipher, 4
certificate, 264
challenge, 385
challenge-and-response protocol, 217, 283, 385
Chaum-van Antwerpen Signature Scheme, 218, 217-223
Chaum-van Heijst-Pfitzmann hash function, 238, 238-241
Chinese remainder theorem, 122, 119-122, 142, 166, 380
Chor-Rivest Cryptosystem, 115
chosen ciphertext cryptanalysis, 25
chosen plaintext cryptanalysis, 25
cipher
block, 20
stream, 20, 20-24, 360
cipher block chaining mode, 83, 83, 267
cipher feedback mode, 83, 85
ciphertext, 1, 20, 378
ciphertext-only cryptanalysis, 25
closure, 332
closure property, 3
code, 194
distance of, 194
dual code, 194
generating matrix, 194
Goppa code, 195
Hamming code, 196
nearest neighbor decoding, 194
parity-check matrix, 194
syndrome, 194
syndrome decoding, 195
coin-flipping by telephone, 400
commutative cryptosystems, 66
commutative property, 3
complete graph, 346
complete multipartite graph, 346, 352, 353
completeness, 286, 386
Composites, 129, 130
computational security, 44
concave function, 56
strictly, 56
concealing, 399
conditional entropy, 59
conditional probability, 45
congruence, 3
conjunctive normal form boolean formula, 337
cryptanalysis, 6
chosen ciphertext, 25
chosen plaintext, 25
ciphertext-only, 25
known-plaintext, 25
cryptogram, 7
cryptosystem, 1
endomorphic, 64
idempotent, 66
iterated, 66
monoalphabetic, 12
polyalphabetic, 13
private-key, 114
probabilistic public-key, 378
product, 64, 64-67
public-key, 114
cyclic group, 123, 183, 187
Data Encryption Standard, 51, 70
description of, 70-78
differential cryptanalysis of, 89, 89-104
dual keys, 110
exhaustive key search, 82
expansion function, 71, 73
initial permutation, 70, 73
key schedule, 71, 75-78
modes of operation, 83, 83-86
S-boxes, 72, 73-75, 82
time-memory tradeoff, 86, 86-89
dealer, 326
deception probability, 305
decision problem, 129, 190
decomposition construction, 354, 355, 353-357
decryption rule, 1, 21, 378
determinant, 16
deterministic algorithm, 129
differential cryptanalysis, 89
characteristic, 98
filtering operation, 101
input x-or, 89
output x-or, 89
right pair, 100
wrong pair, 100
Diffie-Hellman Key Exchange, 270, 270-271
Diffie-Hellman Key Predistribution Scheme, 265, 263-267
Diffie-Hellman problem, 266, 265-267, 275
Digital Signature Standard, 205, 211, 209-213
digram, 25
disavowal protocol, 217
Discrete Logarithm Generator, 383
Discrete Logarithm problem, 162, 163, 164-177, 206, 207, 210, 238, 263, 266, 276, 287, 290, 362, 397, 400, 406
bit security of, 172-177, 400
elliptic curve, 187
generalized, 177, 177-180
in Galois fields, 183
index calculus method, 170-172
ith Bit problem, 173
Pohlig-Hellman algorithm, 169, 166-170
Shanks’ algorithm, 165, 165-166
|


 苏公网安备 32061202001004号
苏公网安备 32061202001004号
